Indume Yene
Platinum Member
- Mar 17, 2008
- 2,950
- 711
Kwa wana Jamii na watanzania wenzangu ulimwenguni kote.
As a responsible citizen nimeamua ku-share elimu ndogo inayohusu Cyber Security ambalo ni eneo langu kiutaalamu.
Kumekuwa na various attacks ambazo zimekuwa zikiwalenga watu mbalimbali duniani hata wakati mwingine bila wenyewe kujua. Watu wengi wamekuwa wakisikia maneno kama virus, malware au spyware. Na vitu kama hivyo ni rahisi kuapata taarifa jinsi ya kujikinga na aina hiyo ya attacks. kadri siku zinavyokwenda attackers wanajifunza mbinu nyingi za kuwashambulia watu bila wenyewe kujua. Na sasa hivi wamekuwa wakiamisha majeshi yao kuelekeza sehemu ambazo ziko nyuma katika mbinu za kujikinga na mashambulizi ya aina hiyo, vile vile sehemu ambayo inaonekana kuanza kutumia IT kwa kasi kupita siku za nyuma.Tanzania ni mojawapo ya nchi Afrika ambayo imeanza kutumia kwa kasi matumizi ya computer and other computing devices. Haya mashambulizi sasa yanaelekezwa huko kwa wingi kwa kuwa majority ya watumiaji wa hizi computing devices hawana uelewa zaidi kuhusu Cyber attacks. Katika mashambulizi haya kuna aina kuu mbili ya mashambulizi.
1. Application attacks.
2. Network attacks.
Kuna sehemu kuu ya mashambulizi katika application imezidi kushika kasi sana duniani. Haya mashambulizi yanaitwa Zero day attacks (sijui kwa kiswahili tunaweza kuita nini ila nitaeleza kwa kifupi). Haya ni mashambulizi ambayo hutumia mwanya mgumu (vulnerability - sijui kama nimepatia kwa kiswahili) ambao hautambuliki kwa mtumiaji wa computer au mtengenezaji (developer) wa programu katika computer na wala hawa watu hawana muda kabisa wa kujiandaa au kujikinga na hayo mashambulizi (ndiyo maana ikaitwa Zero day attack). Sasa mashambulizi kwenye application yanahusisha:
i. Web application attacks
ii. client-side attacks
iii. Buffer overflow attacks
Leo nitazungumzia sehemu ya Web application attacks kwa sababu mashambulizi haya yamekuwa mengi na ni rahisi kwa mtu kutumbukia kwenye hii mitego. Nimesema kuwa nitazungumzia sehemu ya Web application attacks kwa sababu nayo imegawanyika sehemu kama sehemu 4 hivi. Sehemu hizo ni kama ifuatavyo:-
a/. Cross-site script (XSS)
b/. Structured Query Language injection (SQL)
c/. Extensible Markup Language injection (XML)
Sehemu ya leo nitakayogusa ni Cross-site script ambayo imekuwa ni mashambulizi maarufu na ni rahisi kwa client au mtumiaji kuingia kwenye mtego. Sijui lugha rahisi ya Cross-site script kwa kiswahili lakini nitajitahidi kuieleza kadri nielewavyo. Kwa wale waliosoma computer programming wanaelewa nini maana ya script. Kwa wale ambao hawana huo uelewa; script ni program au muendelezo wa maelekezo (instructions) ambayo yanatafsiriwa na kukamilishwa na program nyingine. Kama nilivyotangulia kusema hapo juu kuwa hawa bad guys (attackers) wanaangalia ni wapi wanatumia computing devices kwa wingi na wapi ni rahisi kuwachota watumiaji bila wenyewe kujijua. Sasa basi, katika mashambulizi ya aina hii; attackers wanadumbukiza script kwenye Web application server. Naelewa kuna wengine watajiuliza Web application server ni nini? Kwa lugha nyepesi; Server ni computer au inaweza kuwa ni computer program ambayo ina-manage access na vilevile imeundwa maalum kwa ajili ya kushughulikia (process) mahitaji (requests) na kuwasilisha data kwenye computer zingine ambazo zinaweza kuwa zimeunganishwa au kupitia internet. Sasa tunapozungumzia Web application server nafikiri utakuwa at least umepata mwanga kuwa ni computer maalumu iliyoandaliwa kwa ajili ya kushughulikia mahitaji (requests) na kuwakilisha data kwa muhitaji (user/client). Sasa unapokuwa unatuma hitaji lako kwenye internet hasa Web, inamaana hii server ambayo itakuwa na mafaili maalumu kama vile kurasa za Web (web pages), maandishi (text), picha (graphic files) inashughulikia hitaji lako na kisha kurudisha data kwako kwa muda mfupi.
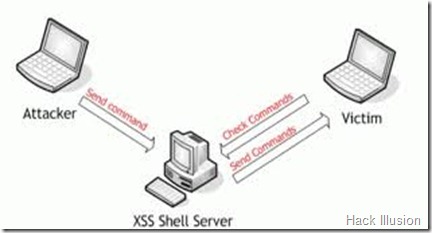
Sasa kinachofanyika ni kuwa huyu mshambuliaji (attacker) atadumbukiza hii script kwenye Web application server. Wewe mtumiaji ambaye unahitahi taarifa kwenye Web hujui lolote kuhusu hayo mashambulizi kwa sababu huna access na hiyo Web application server. Lengo la huyu attacker si kwamba anataka kuidhuru Web server bali anatumia hiyo server kushambulia computer zingine ambazo zitawasiliana na hiyo server kupita mahitaji ambayo mtumiaji anatuma kupitia Web browser kama vile Internet explore, Mozilla n.k. Tuchukulie mfano: Web application server ya web site ambazo zinavuta traffic nying Tanzania kama vile Zoom-Tanzania, Utalii au magazeti. Attacker atakachofanya anadumbukiza script ambayo atakuwa ame-program maelekezo ni nini kifanyike pale computer nyingine itakapotuma mahitaji (requests). Mtumiaji ambaye ni mimi au wewe unapotuma hitaji kupitia browser (web application) tuseme labda kwenye Web site ya Zoom, hiyo browser itatuma hitaji lako kwenda kwenye Zoom Web application server. Sasa kwa kuwa tayari mshambuliaji ameshatumbukiza pale script, hitaji lako litarudi likiwa corrupted bila ya wewe mtumiaji kujua. Hiyo script code itakuwa executed/processed kupitia njia yoyote ambayo browser itatumia kama vile Javascript, Hypertext Markup Languahe (HTML)au Adobe Flash. Na hizi lugha/ njia si rahisi kwao kutambua ni code gani ambayo ni valid au shambulizi.

Ili shambulizi hili litokee, kuna vitu viwili ambavyo vinatakiwa kuwepo.
1. Web site unayotembelea au unayotuma mahitaji (requests) inakubali mtumaji/user kutuma/hitaji bila kukithibitisha.
2. Hiyo Web site inarudisha majibu (response) kwa kutumia hitaji (input)lako bila kubadilisha kwenda kwenye tabia maalum (encoding) kama vile alama n.k
Shambulizi (malicious) likiingia kwenye mashine yako basi attacker anaanza kukomba taarifa zako muhimu (sensitive information) zinazokuwa retained kwenye browser kila unapotembelea sites hizo kama zile za kibenki n.k.
Sasa siku hizi hawa attacker wamegundua jinsi nyingine ya kutuma script. Sasa hivi wanatuma link kupitia kwenye email ya mtu unayemfahamu. Katika email hiyo unakuta hakuna subject na ndani ya body unakuta link. Uki-click unapelekwa kwenye Web site ambayo hata hujui, na mara nyingi unakuta hizo Web site ziko corrupted na attackers wanapata mwanya wa kutuma malicious codes kwenye mashine yako.
Kwa kuwa topic bado inaendelea, nitakuja tena na njia ya kujikinga na Application attacks. Ila kama utaona email imekuja ikiwa na link bila maelezo kutoka kwa muhusika, wala husijaribu kui-click/ fungua. Utakuwa unafungua mlango kwa attackers kuingia kwenye mashine yako bila ya wewe kujua.
Kama una swali, jisikie huru kuuliza.
Nakutakieni siku njema na kuweni waangalifu katika kufungua barua pepe.
Dawati la Usalama katika Mtandao.
As a responsible citizen nimeamua ku-share elimu ndogo inayohusu Cyber Security ambalo ni eneo langu kiutaalamu.
Kumekuwa na various attacks ambazo zimekuwa zikiwalenga watu mbalimbali duniani hata wakati mwingine bila wenyewe kujua. Watu wengi wamekuwa wakisikia maneno kama virus, malware au spyware. Na vitu kama hivyo ni rahisi kuapata taarifa jinsi ya kujikinga na aina hiyo ya attacks. kadri siku zinavyokwenda attackers wanajifunza mbinu nyingi za kuwashambulia watu bila wenyewe kujua. Na sasa hivi wamekuwa wakiamisha majeshi yao kuelekeza sehemu ambazo ziko nyuma katika mbinu za kujikinga na mashambulizi ya aina hiyo, vile vile sehemu ambayo inaonekana kuanza kutumia IT kwa kasi kupita siku za nyuma.Tanzania ni mojawapo ya nchi Afrika ambayo imeanza kutumia kwa kasi matumizi ya computer and other computing devices. Haya mashambulizi sasa yanaelekezwa huko kwa wingi kwa kuwa majority ya watumiaji wa hizi computing devices hawana uelewa zaidi kuhusu Cyber attacks. Katika mashambulizi haya kuna aina kuu mbili ya mashambulizi.
1. Application attacks.
2. Network attacks.
Kuna sehemu kuu ya mashambulizi katika application imezidi kushika kasi sana duniani. Haya mashambulizi yanaitwa Zero day attacks (sijui kwa kiswahili tunaweza kuita nini ila nitaeleza kwa kifupi). Haya ni mashambulizi ambayo hutumia mwanya mgumu (vulnerability - sijui kama nimepatia kwa kiswahili) ambao hautambuliki kwa mtumiaji wa computer au mtengenezaji (developer) wa programu katika computer na wala hawa watu hawana muda kabisa wa kujiandaa au kujikinga na hayo mashambulizi (ndiyo maana ikaitwa Zero day attack). Sasa mashambulizi kwenye application yanahusisha:
i. Web application attacks
ii. client-side attacks
iii. Buffer overflow attacks
Leo nitazungumzia sehemu ya Web application attacks kwa sababu mashambulizi haya yamekuwa mengi na ni rahisi kwa mtu kutumbukia kwenye hii mitego. Nimesema kuwa nitazungumzia sehemu ya Web application attacks kwa sababu nayo imegawanyika sehemu kama sehemu 4 hivi. Sehemu hizo ni kama ifuatavyo:-
a/. Cross-site script (XSS)
b/. Structured Query Language injection (SQL)
c/. Extensible Markup Language injection (XML)
Sehemu ya leo nitakayogusa ni Cross-site script ambayo imekuwa ni mashambulizi maarufu na ni rahisi kwa client au mtumiaji kuingia kwenye mtego. Sijui lugha rahisi ya Cross-site script kwa kiswahili lakini nitajitahidi kuieleza kadri nielewavyo. Kwa wale waliosoma computer programming wanaelewa nini maana ya script. Kwa wale ambao hawana huo uelewa; script ni program au muendelezo wa maelekezo (instructions) ambayo yanatafsiriwa na kukamilishwa na program nyingine. Kama nilivyotangulia kusema hapo juu kuwa hawa bad guys (attackers) wanaangalia ni wapi wanatumia computing devices kwa wingi na wapi ni rahisi kuwachota watumiaji bila wenyewe kujijua. Sasa basi, katika mashambulizi ya aina hii; attackers wanadumbukiza script kwenye Web application server. Naelewa kuna wengine watajiuliza Web application server ni nini? Kwa lugha nyepesi; Server ni computer au inaweza kuwa ni computer program ambayo ina-manage access na vilevile imeundwa maalum kwa ajili ya kushughulikia (process) mahitaji (requests) na kuwasilisha data kwenye computer zingine ambazo zinaweza kuwa zimeunganishwa au kupitia internet. Sasa tunapozungumzia Web application server nafikiri utakuwa at least umepata mwanga kuwa ni computer maalumu iliyoandaliwa kwa ajili ya kushughulikia mahitaji (requests) na kuwakilisha data kwa muhitaji (user/client). Sasa unapokuwa unatuma hitaji lako kwenye internet hasa Web, inamaana hii server ambayo itakuwa na mafaili maalumu kama vile kurasa za Web (web pages), maandishi (text), picha (graphic files) inashughulikia hitaji lako na kisha kurudisha data kwako kwa muda mfupi.
Sasa kinachofanyika ni kuwa huyu mshambuliaji (attacker) atadumbukiza hii script kwenye Web application server. Wewe mtumiaji ambaye unahitahi taarifa kwenye Web hujui lolote kuhusu hayo mashambulizi kwa sababu huna access na hiyo Web application server. Lengo la huyu attacker si kwamba anataka kuidhuru Web server bali anatumia hiyo server kushambulia computer zingine ambazo zitawasiliana na hiyo server kupita mahitaji ambayo mtumiaji anatuma kupitia Web browser kama vile Internet explore, Mozilla n.k. Tuchukulie mfano: Web application server ya web site ambazo zinavuta traffic nying Tanzania kama vile Zoom-Tanzania, Utalii au magazeti. Attacker atakachofanya anadumbukiza script ambayo atakuwa ame-program maelekezo ni nini kifanyike pale computer nyingine itakapotuma mahitaji (requests). Mtumiaji ambaye ni mimi au wewe unapotuma hitaji kupitia browser (web application) tuseme labda kwenye Web site ya Zoom, hiyo browser itatuma hitaji lako kwenda kwenye Zoom Web application server. Sasa kwa kuwa tayari mshambuliaji ameshatumbukiza pale script, hitaji lako litarudi likiwa corrupted bila ya wewe mtumiaji kujua. Hiyo script code itakuwa executed/processed kupitia njia yoyote ambayo browser itatumia kama vile Javascript, Hypertext Markup Languahe (HTML)au Adobe Flash. Na hizi lugha/ njia si rahisi kwao kutambua ni code gani ambayo ni valid au shambulizi.
Ili shambulizi hili litokee, kuna vitu viwili ambavyo vinatakiwa kuwepo.
1. Web site unayotembelea au unayotuma mahitaji (requests) inakubali mtumaji/user kutuma/hitaji bila kukithibitisha.
2. Hiyo Web site inarudisha majibu (response) kwa kutumia hitaji (input)lako bila kubadilisha kwenda kwenye tabia maalum (encoding) kama vile alama n.k
Shambulizi (malicious) likiingia kwenye mashine yako basi attacker anaanza kukomba taarifa zako muhimu (sensitive information) zinazokuwa retained kwenye browser kila unapotembelea sites hizo kama zile za kibenki n.k.
Sasa siku hizi hawa attacker wamegundua jinsi nyingine ya kutuma script. Sasa hivi wanatuma link kupitia kwenye email ya mtu unayemfahamu. Katika email hiyo unakuta hakuna subject na ndani ya body unakuta link. Uki-click unapelekwa kwenye Web site ambayo hata hujui, na mara nyingi unakuta hizo Web site ziko corrupted na attackers wanapata mwanya wa kutuma malicious codes kwenye mashine yako.
Kwa kuwa topic bado inaendelea, nitakuja tena na njia ya kujikinga na Application attacks. Ila kama utaona email imekuja ikiwa na link bila maelezo kutoka kwa muhusika, wala husijaribu kui-click/ fungua. Utakuwa unafungua mlango kwa attackers kuingia kwenye mashine yako bila ya wewe kujua.
Kama una swali, jisikie huru kuuliza.
Nakutakieni siku njema na kuweni waangalifu katika kufungua barua pepe.
Dawati la Usalama katika Mtandao.